Hi there, I’m Joy — glad you stopped by! 😊 My full Chinese name is 董珏初 Juechu (pronounced roughly ge-ü-e, chew), but Joy works just fine in everyday life.
Bio:
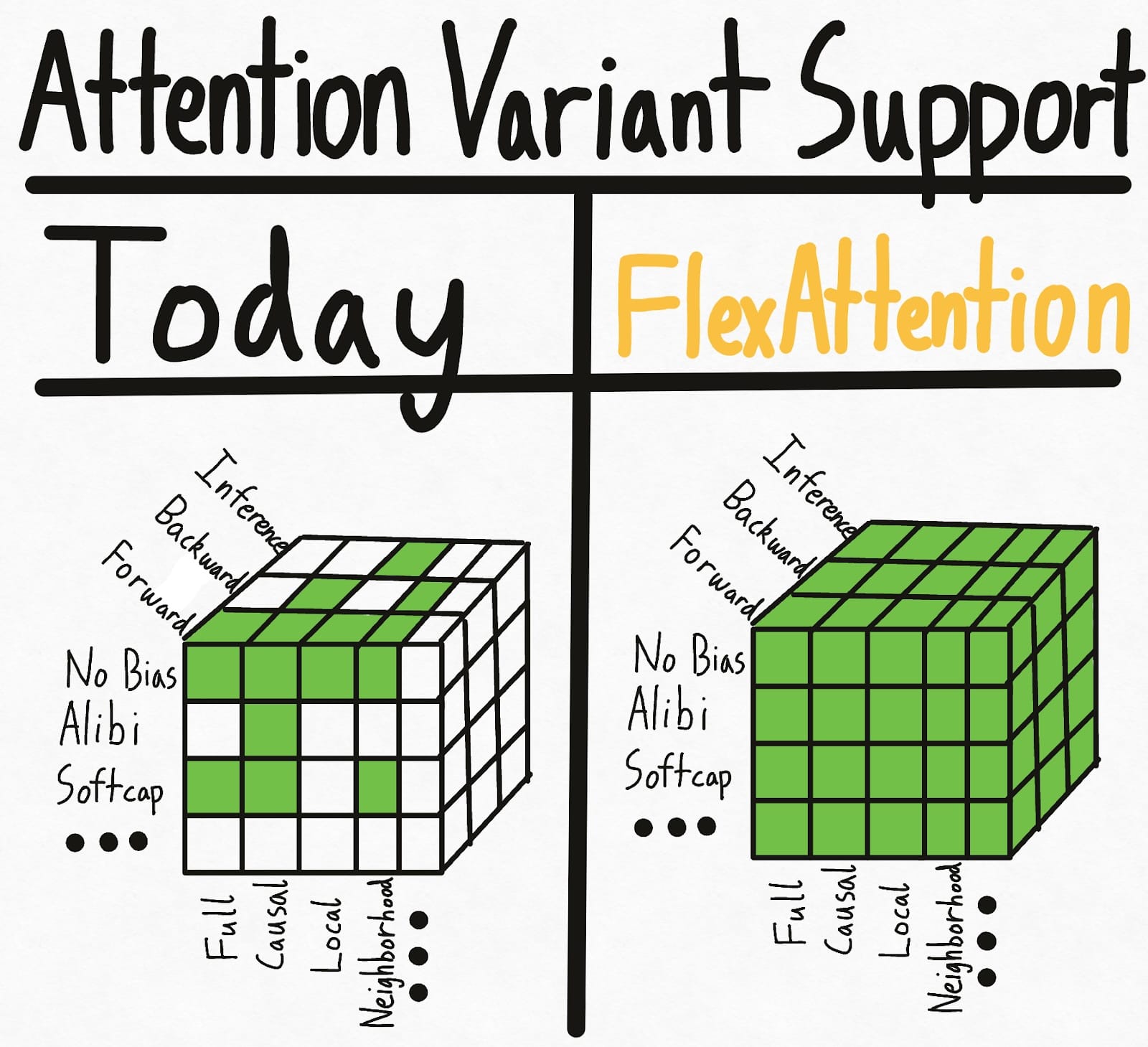
Joy Dong is a PhD Candidate at the University of Michigan specializing in computer architecture and GPU programmability, where she is advised by Prof. Satish Narayanasamy. Her research focuses on building the software stack for the next generation of AI, specifically optimizing GPU kernels to make large-scale machine learning more efficient and accessible. She previously worked on FlexAttention and Helion at Meta PyTorch and CuTe DSL ecosystem at Nvidia.